Security incident response plan template provides a structured framework to identify, contain and recover from security breaches. As a trusted tool for Security Company Melbourne, it ensures swift, coordinated action across all teams.
Understanding Security Incident Response Plan Template
A template this comprehensive slots neatly into your organisation’s risk management framework and meets all licence requirements. When Australian businesses formalise their incident management routines, they reduce downtime and unexpected costs.
Key building blocks include:
- Preparation & Scope Definition
- Roles & Responsibilities
- Detection & Notification Processes
- Containment, Eradication & Recovery
- Post-Incident Review & Lessons Learned
| Benefit | Description |
|---|---|
| Faster Containment | Streamlines decisions to isolate threats quickly |
| Clear Communication | Clarifies notification paths for staff, clients and regulators |
| Regulatory Compliance | Documents actions to meet licence and legislative standards |
Imagine a retail complex in Melbourne where an alarm breach triggered mobile patrols, IT teams and management. They used this template to resolve the incident in under 45 minutes.
For expert support with incident logging or escalation, see our Incident Management services.
Dive deeper into controls via our Risk and Security Management guide.
Real-World Application
A NSW construction firm customised the template to include third-party vendor logs and site patrol records. That tweak cut resolution time by 40%, while meeting ASIAL guidelines.
Consistency and clarity in incident reporting build trust and reduce confusion during emergency responses
For advanced support, explore professional Incident Response services.
In Brisbane, a strata manager streamlined vendor alerts and legal reporting after a perimeter breach. Stakeholder inquiries dropped by 50%.
Ready to bring your plan to life? Book support at our service booking page.
Preparing Stakeholders And Resources
Early engagement secures executive sponsorship and aligns resources. This upfront investment saves confusion when a breach occurs.
Start by:
- Identifying critical assets and mapping data flows
- Mapping communication channels across IT, management, HR and legal
- Assigning roles and responsibilities with up-to-date contact details
- Securing budget for detection tools, staff training and external expertise
Conducting A Basic Risk Assessment
Rank assets by:
- Sensitivity
- Potential financial or reputational loss
- Recovery time objectives
Feed insights into your plan to address high-priority gaps first. Our security audit service pinpoints vulnerabilities and offers tailored analytics.
Align your risk profile with licence obligations and local compliance standards. With clear handoffs, forming the incident response team becomes seamless.
A well-documented risk profile helps teams act decisively when incidents occur
Building Your Incident Response Team
Choose an Incident Manager to steer workflows. Include:
- In-house IT specialists, communications and legal advisors
- External partners like forensic analysts and crisis PR consultants
- Defined escalation paths and toolkits (phone trees, secure chat)
One Melbourne tech company aligned its Essential Eight maturity level with ASIAL guidelines and ran real-world drills to refine their playbook.
Explore our guide on private security contractors in Australia to see how external teams integrate with your response model.
Don’t forget to document:
- Primary and backup communication methods (SMS alerts, encrypted messaging)
- Notification triggers, escalation thresholds and authorisations under the Notifiable Data Breaches scheme
These steps accelerate reporting and minimise legal risk.
Breaking Down Template Components
Each section helps Security Company Melbourne coordinate incident management and recovery. Clear organisation ensures every team member knows their role.
Recent data shows Australia saw a 25% rise in data breaches during 2024, yet only 45% of organisations had a formal IRP. For details, explore Riskonnect’s findings.
Purpose And Scope
Define activation triggers with:
- A concise purpose statement detailing incident types
- Scope notes on systems, sites and critical data assets
- Response goals (containment timeframes, notification deadlines)
In a Sydney retail centre, any POS breach exposing card data was explicitly covered. Finance teams often add data mapping to fast-track regulator reports.
Roles And Responsibilities
Clear roles speed decisions. Define:
- Incident Manager: coordinates tasks and briefs executives
- IT Lead: handles detection systems and initial analysis
- Communications Liaison: crafts internal and external messages
- HR Liaison: supports staff welfare and shift adjustments
- Legal Advisor: manages compliance and notifications
A Perth finance firm added a Vendor Liaison to streamline third-party audits.
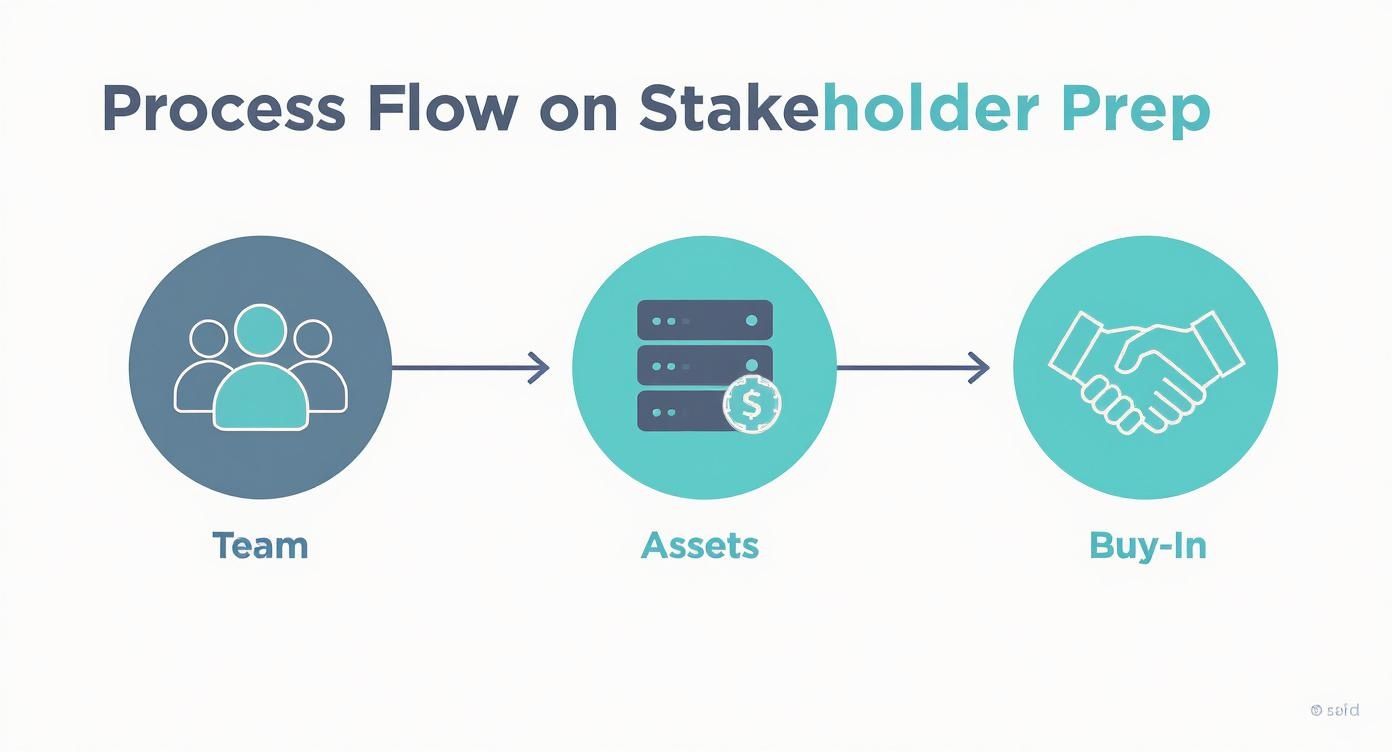
Visualising Stakeholder Preparation
This infographic maps asset mapping, team assembly and executive buy-in—crucial steps that shave minutes off response time.
Detection Workflows And Communication Protocols
A clear workflow ties alerts to actions:
- Sensor or log alert flagged by your SIEM
- Triage by the IT Lead within 15 minutes
- Cascade notifications to management and legal
Many teams integrate CCTV and alarm feeds to improve threat detection. For more, see our comprehensive guide on security systems monitoring.
Communication rules:
- Email groups with read-receipts for urgent alerts
- SMS pings for off-shift staff
- Secure chat rooms uniting tech experts and external responders
A Melbourne retail chain linked POS alerts to its IRP dashboard, cutting 30% of false positives and saving 40 minutes per incident.
Containment And Recovery Steps
Isolate threats and restore operations:
- Network segmentation to quarantine suspicious IPs
- Activation of backup systems for critical servers
- Step-by-step guides for scenarios like ransomware
Always verify backups, test restores and reconnect production only after validation. NSW organisations customise templates to trigger licence-driven mobile patrols.
Key Sections Of An IRP Template
| Template Section | Description | Key Benefit |
|---|---|---|
| Purpose And Scope | Defines covered incidents | Sets activation triggers |
| Roles And Responsibilities | Lists ownership and communication leads | Speeds decision making |
| Detection Workflows | Outlines alert sources and triage steps | Ensures prompt identification |
| Communication Protocols | Specifies notification methods and timing | Reduces stakeholder uncertainty |
| Containment And Recovery | Details isolation and restoration steps | Minimises downtime and data loss |
| Post Incident Review | Guides analysis and improvement after incidents | Drives continuous refinement |
Post Incident Review
Hold a lessons-learned workshop within two weeks:
- Rebuild the incident timeline
- Conduct root-cause analysis
- Assign follow-up actions
- Schedule policy updates
Align with Fair Work Australia guidelines for staff notifications. Track metrics like mean time to detection and repair to build trust.
A well broken-down template ensures every team member knows their role and reduces response time significantly
Customising Your Incident Response Plan Template
Choosing the right format makes a real difference. Options include:
- Fillable PDF with embedded fields
- Spreadsheet with tabbed sheets for workflows and logs
- Software platform to automate alerts and manage versions
- Combined approach using PDF exports from software
Our consultants often recommend spreadsheets for live tracking—just watch for clutter.
Industry-Specific Fields
Custom fields ensure you capture critical data:
- Third-party Vendor Logs with timestamps
- Licence Number and Class fields for compliance
- Essential Eight maturity level indicators
A comprehensive small business disaster recovery plan template can inspire further customisation.
Explore our event risk assessment template for related forms.
Matching Maturity Levels
Link each section to an Essential Eight maturity goal:
- Rate current versus target maturity levels
- Adjust fields to capture proof of control implementation
- Include a summary sheet highlighting gaps
Local licence rules often call for extra approval stamps—overlooking these can incur fines.
A customised template bridges technical controls and regulatory checks for faster, compliant responses.
Pitfalls And Solutions
Keep initial forms lean:
- Limit to five mandatory entries on the first page
- Use conditional logic to reveal extra sections when needed
- Highlight urgent actions with colour coding
Sync vendor contacts with your event risk assessment tool to avoid outdated details.
Sample Field Layout
| Field Name | Example Entry |
|---|---|
| Vendor Log Timestamp | 2024-09-15 14:32 |
| Licence Class | Crowd Control |
| CCTV Reference | CAM-05-17 |
Collaboration Settings
Role-based permissions keep your template secure:
- Read-only views for general staff
- Email notifications for changes
- Edit logs for full traceability
Version Control
Label updates with version numbers and dates:
- Tag major revisions like v1.0, v1.1 and v2.0
- Archive old templates in a secure folder
- Review history quarterly to retire outdated formats
Contact us for tailored walkthroughs that meet Essential Eight requirements.
Maintaining And Testing Your Response Plan
Routine testing slashes repair time and proves your reliability as a security partner in Melbourne.
Quarterly Mock Drills
Run mock drills every three months:
- Define realistic scenarios (ransomware, supply-chain breach)
- Involve IT, operations, comms and leadership
- Set targets for detection, containment and communication
- Debrief to capture lessons and action points
Assign a drill lead to coordinate scheduling, environments and feedback.
Updating Key Plan Components
Keep your plan aligned:
- Verify primary and backup contacts monthly
- Refresh ransomware playbooks with new TTPs
- Incorporate real vendor incident logs into supply-chain guides
- Align procedures with ASIAL’s continuous improvement guides
- Consult our Guide on Getting a Security Licence
Embedding Review Culture
Post-exercise workshops spot gaps early:
- Convene within two weeks of each drill or breach
- Analyse timelines, decisions and communications
- Log action items and set update deadlines
- Share changes with teams and executives
Australian data shows a 48% spike in breaches last year, yet only 35% tested IRPs fully. Australian Data Breaches 2025 Surge reveals recovery stretched to 28 days without testing.
A tested response plan halves recovery time and boosts stakeholder confidence.
Maintenance Schedule For IRP
| Practice | Frequency | Benefit |
|---|---|---|
| Mock Drills | Quarterly | Exposes process gaps quickly |
| Contact Updates | Monthly | Ensures accurate alerts |
| Playbook Reviews | Biannually | Keeps scenarios current |
| Post-Incident Workshops | After event | Embeds lessons learned |
Training And Ownership
Training ensures clarity in high-pressure situations:
- Run incident response training twice a year
- Assign ownership of each IRP component
- Use scenario-based workshops to embed playbook steps
An Adelaide retail client cut recovery time by 35% after naming owners and reinforcing skills.
Ready to maintain and test your plan? Book with our experts: Service Booking.
Overcoming Common Response Plan Pitfalls
Small oversights can stall your response. A lean, updated plan prevents delays.
Identifying Outdated Contacts
A Sydney retailer found 30% of emergency numbers were obsolete. They moved to a shared directory synced with HR—now 100% of alerts reach active responders.
Set a monthly review and follow ASIAL guidelines on staffing protocols.
A lean contact directory updated regularly prevents delays when every second counts
Simplifying Roles And Steps
Complex procedures can trip up teams. A Melbourne finance firm trimmed its playbook from 12 pages to three action cards and just three roles. Next drill: mean time to recovery dropped by 35%.
- Map only must-do tasks per role
- Use bullet points or quick-reference checklists
- Colour-code steps for instant clarity
- Store detailed procedures separately
Ensuring Drills Expose Gaps
Regular practice reveals blind spots:
- Rotate scenarios: ransomware, supply-chain, insider threats
- Debrief immediately to lock in fresh insights
- Track action items in your post-incident log
A small, lean and actionable template is far more effective than a bulky document.
Spotting Gaps Early
A Perth logistics operator’s drill showed missing vendor contacts. Adding them improved supplier communication dramatically.
- Use digital surveys for instant feedback
- Present drill audits quarterly to executives
- Benchmark against ASIAL’s continuous improvement checklists
- Update your template promptly
A living template that evolves with each drill keeps teams engaged and incident-ready
Our trainers help integrate these tips with hands-on workshops. Check our training sessions and security audit service to verify contact lists and workflows.
Frequently Asked Questions
A thorough security incident response plan covers all stages from detection to post-mortem. This approach keeps teams aligned when every second counts.
Core Elements Every Template Needs
- Purpose and Scope: Defines incident triggers
- Roles and Responsibilities: Assigns duties across IT, security, legal and HR
- Communication Protocols: Integrates with Notifiable Data Breaches requirements
- Containment Workflows: Uses predefined checklists and escalation paths
Ideal Testing Cadence
Most organisations find a quarterly mock scenario balances realism and resources. Smaller operations may prefer biannual tabletop sessions, while larger enterprises run monthly simulations.
Tailoring For Organisation Size
Small businesses benefit from a streamlined template focused on priority assets and compliance triggers. Larger enterprises layer in audit trails and multi-level escalation to satisfy licence obligations and ASIAL guidelines.
Embedding Compliance Triggers
Automated reminders for Notifiable Data Breaches deadlines under the Privacy Act prevent missed reporting. Link prompts to your risk register and audit calendar.
Periodic testing and compliance checks turn your template into a living document that adapts to evolving threats
Ready to refine your security incident response plan template? Secure your incident response planning session with ABCO Security Services Australia today.